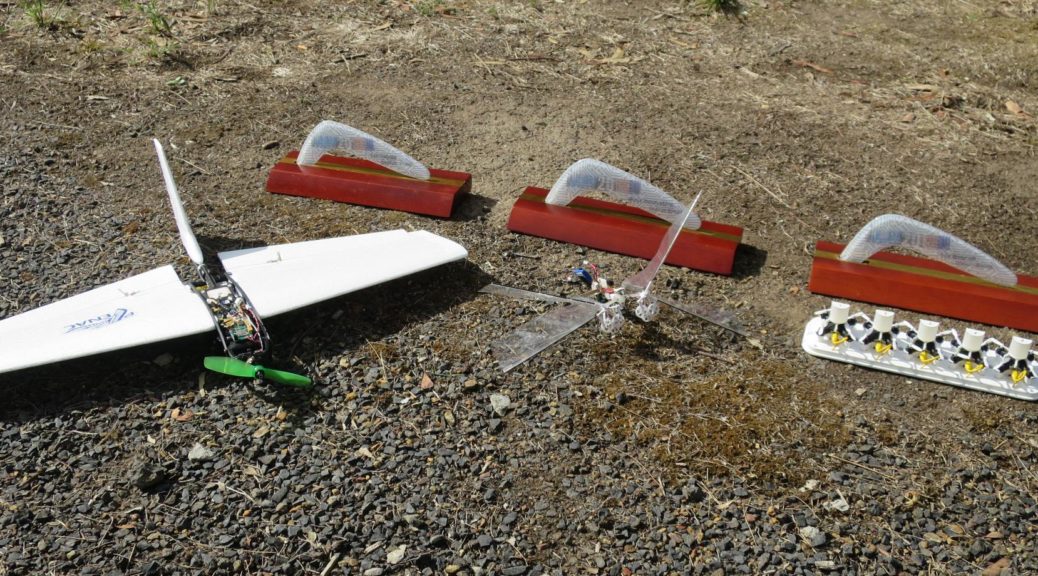
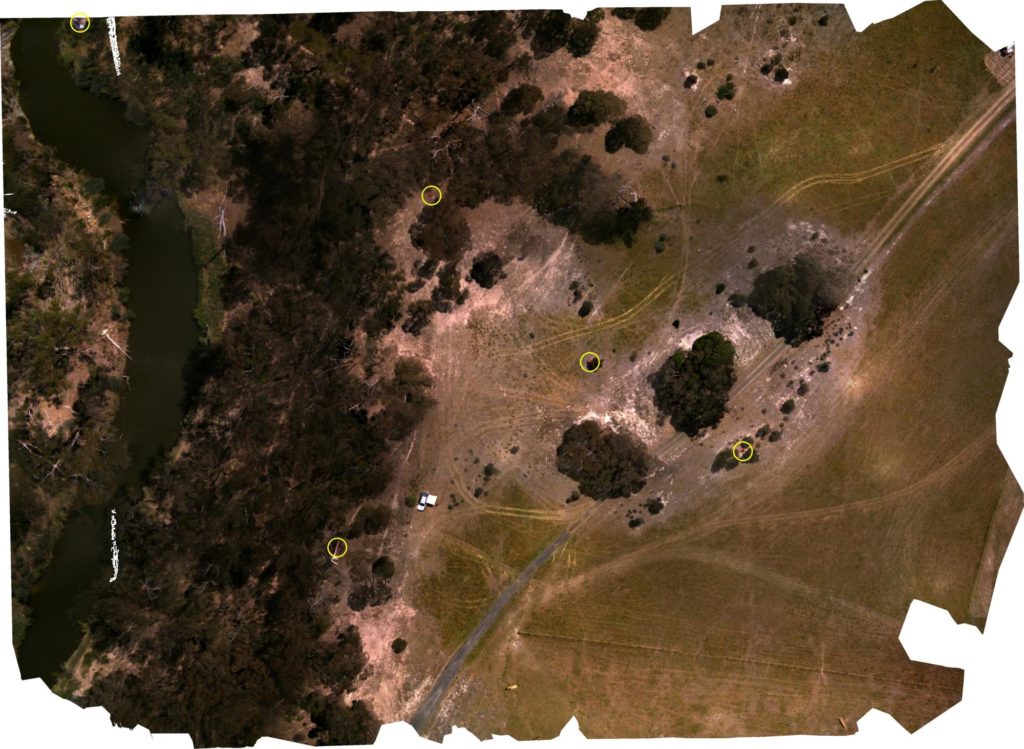
The International Conference and Competition on MAV was organized by TUDelft mid-September 2022. The ENAC took part to the outdoor competition, a package delivery challenge, with several multi-rotors and a hybrid tail-sitter, all powered by Paparazzi.
They won the competition with a quite large amount of points. Nevertheless, all teams performed well with some innovative platforms.
Several papers have been presented to the conference by the ENAC team and the other participants. The proceedings are freely available on the conference website.